During our recent webinar (CMMC 2.0 Explained: What Contractors Need to Prepare for in 2026), panelists shared some often overlooked tips and warnings for contractors that usually don’t get talked about in many CMMC discussions.
While larger contractors may be fully aware of our tips below, the same might be not true for non-traditional contractors, commercial businesses that do just some work in the government space, or small businesses that are newer to contracting as part of the DoD supply chain.
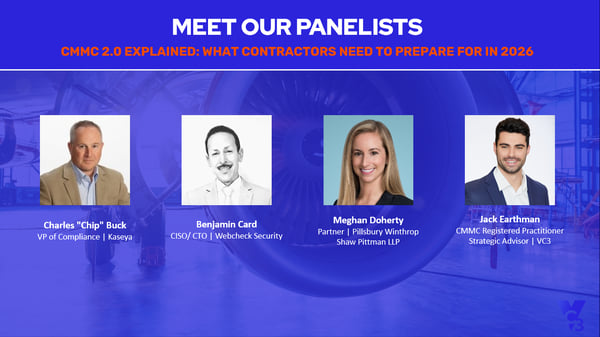
Our webinar panel included:
- Charles "Chip" Buck, VP of Compliance, Kaseya
- Benjamin Card, CISO / CTO, WebCheck Security
- Meghan Doherty, Partner, Pillsbury Winthrop Shaw Pittman LLP
- Jack Earthman, Strategic Advisor, VC3
- Mike Snyder, Executive Director, Ecosystem Engagement, CyberAB
We’ve distilled their most actionable insights below.
1. The Real CMMC Risk in 2026: Not Getting Assessed in Time
Right now, the pool of CMMC Third-Party Assessor Organizations (C3PAOs) is still small relative to the size of the defense industrial base. Because audits are not currently mandatory, many organizations are inevitably procrastinating and not getting in line to have these audits performed.
But think about the upcoming problem. It’s slow to build up C3PAOs, so a wave of them will not magically appear. That means when the time comes for mandatory audits, the supply of C3PAOs will struggle to meet demand from thousands of DoD contractors.
As a result, organizations that wait to become CMMC-compliant may find themselves boxed out—not because they can’t meet requirements, but because they can’t get on an assessor’s calendar fast enough when certification becomes a gating factor for contract eligibility.
Getting in line right now for a C3PAO audit is a competitive advantage. Otherwise, there is a risk that you will be left with no work because you haven't been assessed and certified.
Takeaway: Get on a C3PAO’s calendar sooner rather than later. Don’t wait until everything is perfect in your IT environment. You can actively remediate while also engaging assessors—and it’s often expected that you will still have items to fix after an audit.
2. Scope Sprawl Is a Silent Budget Killer
Scope sprawl is a tendency for companies to accept their current Controlled Unclassified Information (CUI) flow as fixed when it can actually be redesigned. Many organizations unintentionally expand scope through convenience strategies such as shared drives, broad access groups, mixed environments, unmanaged endpoints, or informal data handoffs.
You can drastically reduce your compliance effort if you reduce the scope of what touches CUI. The fewer people, systems, and locations that touch CUI, the smaller—and cheaper—your compliance footprint becomes.
Practical ways to shrink scope include:
- Mapping your full CUI lifecycle including how it enters, moves, is stored, and exits your environment.
- Eliminating “nice-to-have visibility” access to CUI (especially outside roles that truly require access).
- Segmenting environments so that only the systems and users that actually handle CUI are subject to full CMMC requirements, rather than upgrading your entire environment unnecessarily.
- Having a single team or function responsible for CUI intake, storage, and controlled distribution so that you decrease overall risk and various departments don’t handle CUI inconsistently.
You may also have to re-scope as your business evolves with new business processes, products, services, or a merger. Every time something like this happens, make sure that you re-scope.
Takeaway: Before you buy another tool or write another policy, tighten your scope. It’s the most direct lever for reducing remediation cost and audit complexity.
3. An Overlooked Step: Vendor and Partner Accountability Mapping
It’s hard enough to make sure your own data is protected. However, you need to worry about more than just yourself as you partner with other subcontractors and use vendors to support your work. Within this ecosystem, there are flow down requirements where you must make sure that partners and vendors apply the same CMMC standards protecting the security of any CUI that they touch.
It helps to take an inventory of who is involved and what they own before remediation starts. That means documenting:
- Which vendor provides which control capability (and whether they operate it or only sell it)
- Who owns policy creation vs. implementation vs. evidence collection
- Who is responsible for closing each gap (such as your internal team, an MSP/MSSP, a consultant, a software provider, etc.)
- How you will track and prove changes during an assessment
Takeaway: Build an accountability matrix early. If you can’t clearly answer, “Who owns this control and how will we prove it?” then you’re not ready for remediation—or an audit.
4. Continuous Compliance Isn’t Just Maintenance—It’s a Business Discipline
Once you achieve compliance, the instinct is to breathe a sigh of relief. Our panel urged the opposite.
Annual executive attestations and recurring reassessments mean you can’t treat CMMC as a one-and-done project. The best insight about ongoing compliance from our panelists wasn’t about requirements—it was about drift.
The biggest sources of drift that can affect your ongoing compliance journey include:
- Employee onboarding and offboarding (including accounts, access, MFA, and device control)
- Customer onboarding and offboarding (including data retention, data disposal, and separation processes)
- Business changes that quietly re-expand scope (such as new workflows, new tools, M&A, and new locations)
Ongoing compliance should be treated as a business discipline. It’s highly recommended to help operationalize compliance by leveraging a Governance Risk & Compliance (GRC) tool to maintain policies and evidence collection. The companies that will handle CMMC requirements best are the ones that turn compliance into repeatable operations instead of merely a compliance binder.
Takeaway: If compliance is not embedded within your operations, it will quietly decay—and you may not discover how much decay until another audit approaches.
5. The Legal Exposure You Can’t Patch: Annual Attestations and False Claims Risk
The final overlooked insight was a reality check that’s still missing from many CMMC conversations. Noncompliance with CMMC isn’t just “IT risk.” It’s legal risk—as seen by two major issues.
- CUI isn’t always clearly marked: Many contractors assume CUI will arrive labeled and consistent. In practice, markings can be inconsistent, legacy-labeled, or even missing. Despite this, contractors still have obligations to identify and protect any CUI that they handle—including CUI they generate.
- Inaccurate attestations create False Claims Act exposure: Annual attestations by senior officials at your organization aren’t procedural fluff. From a legal perspective, certifying compliance while you’re materially noncompliant can create pathways to the government investigating you using the False Claims Act. An inaccurate certification tied to payment, contract performance, or renewal is legally dangerous—and the US government has demonstrated active enforcement in these areas.
Takeaway: Treat compliance representations like financial statements. Validate them, document them, and ensure leadership understands what they’re signing. Make sure your compliance profile is up to date, that any certifications you're making are accurate, and that you're staying in compliance.
Final Thought: CMMC Readiness Is Becoming a Market Signal
A subtle theme throughout the panel discussion was that CMMC isn’t only about security. CMMC compliance is also becoming a capability signal across the defense supply chain. The companies that treat compliance as an operational advantage—not as an annual scramble—will be best positioned for 2026 and beyond.
Want help scoping, planning, or operationalizing CMMC readiness? VC3 can help you build a prioritized remediation roadmap, reduce compliance scope, and maintain audit readiness over time. Reach out to us today.