Filter by
Blog
|
10 min read
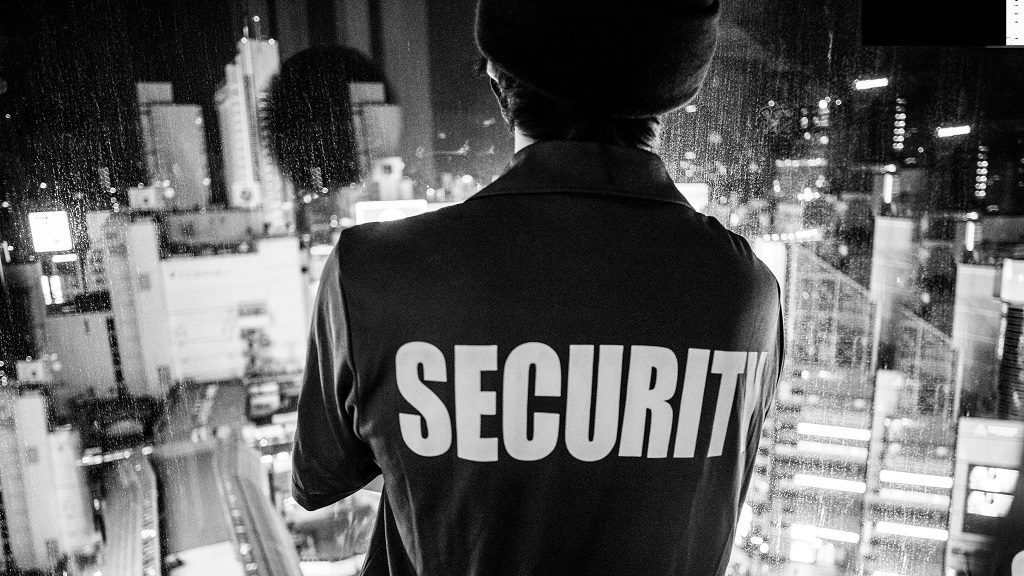
The Threat from Inside: Why Your Cybersecurity Tools Must Now Detect as Wel...
Imagine you're in charge of the physical security of a large office building. Your job is to keep bad people out. Excite...
Read More

Blog
|
3 min read
Four Devastating Things that Happen to Towns and Cities with Uncertain Data...
Data backup may be the most important technology component for a municipality. Yet, many towns and cities still operate ...
Read More

Blog
|
3 min read
Top 3 Best IT Practices: Advice from a Non-Technology Expert
Are you someone without a technical background, and little to no knowledge of technology? Do you find yourself constantl...
Read More

Blog
|
6 Min Read
14 Cybersecurity Myths and Misconceptions
Common cybersecurity myths needing to be debunked to ensure you're properly approaching and reducing your risk around cy...
Read More

Blog
|
3 min read
Critical Microsoft Exchange Vulnerability Illustrates Importance of Cyber T...
Last Wednesday, the Cybersecurity and Infrastructure Security Agency (CISA), a federal agency overseen by the Department...
Read More

Blog
|
2 min read
Water Supply Attack Illustrates Security Lessons for Municipalities
During the first week of February in Oldsmar, Florida, a hacker tried to poison the city's water supply by increasing th...
Read More
